In the competitive landscape of rolletto online casinos, the login gateway is not merely a point of entry but a critical security checkpoint. This whitepaper provides a exhaustive technical analysis of the Rolletto login ecosystem, encompassing the Rolletto login process, its integration with the rolletto app, underlying security architecture, and advanced troubleshooting methodologies. Understanding this system is essential for both new users and seasoned players to ensure uninterrupted access and protect their digital assets.
Before You Start: Essential Checklist
Prior to engaging with the Rolletto platform, verify these prerequisites to streamline your login experience:
- A stable internet connection (minimum 5 Mbps for the rolletto app).
- A valid email address not associated with any existing Rolletto account.
- Knowledge of your device’s operating system (iOS, Android, Windows) for app compatibility.
- Preparation of a strong password (12+ characters, mixed case, symbols, numbers).
- Access to your email inbox for verification links.
- Understanding of basic SSL/TLS indicators (padlock icon in browser).
- Familiarity with your preferred payment method for post-login verification.
- A backup authentication method (e.g., phone number) for account recovery.
Registration: The Foundation of Login
The Rolletto login credential set is created during registration. This process involves several technical steps that establish your digital identity on the platform.
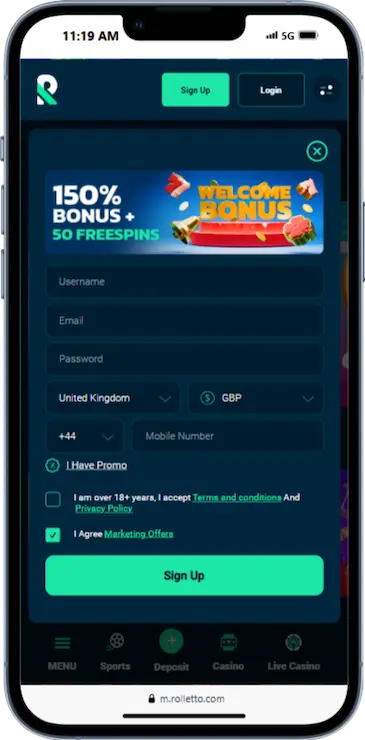
The procedure is sequential: 1) Enter email (becomes your login username), 2) Create a password (hashed and stored securely), 3) Provide personal details (for account linking), 4) Confirm terms, and 5) Click verification link sent to your email. This email verification acts as the first login attempt, authenticating your email ownership. Failure here often stems from email server delays or incorrect address entry.
Login Mathematics: Calculating Security & Risk
Login security can be modeled mathematically. Consider password entropy (E) calculated as E = L * log₂(R), where L is password length and R is the size of the character set. For a Rolletto password using 94 possible characters (mixed case, numbers, symbols) at 12 length, E = 12 * log₂(94) ≈ 78 bits. This entropy value determines resistance to brute-force attacks. Furthermore, the probability of successful unauthorized login (P) can be approximated if we know attack rate (A) and lockout threshold (T). For example, if Rolletto’s system locks after 5 failed attempts (T=5) and an attacker tries 100 attempts/hour (A=100), P ≈ (5/100) * (1/24) for a day-scale attack, considering rate limiting. Users should aim for high entropy passwords to minimize P.
| Login Parameter | Technical Specification | User Impact |
|---|---|---|
| Authentication Method | Email & Password (SHA-256 hashing), optional 2FA | Determines login speed and security level |
| Session Duration | Default 30 minutes, extendable up to 24 hours in rolletto app | Affects convenience vs. security trade-off |
| Failed Attempt Lockout | 5 attempts triggers 15-minute temporary block | Prevents brute-force but may inconvenience legitimate users |
| Cross-Platform Sync | Login session shared between rolletto online web and app via tokens | Enables seamless switching but requires token validation |
| Password Update Policy | Mandatory every 180 days, optional anytime | Enforces security freshness |
Banking Integration: How Login Affects Financial Access
Your Rolletto login credentials are directly linked to payment method authorization. When initiating a withdrawal, the system re-authenticates your session using the same login tokens. This means a compromised login can lead to financial leakage. The rolletto app particularly uses device biometrics (fingerprint, face ID) as a login supplement for payment confirmations, adding an extra layer. However, if you login from a new device without biometric setup, you may face additional security checks when accessing banking features. This integration ensures that financial operations are tied to a verified login state, preventing unauthorized transactions.
Security Deep Dive: Encryption, 2FA, and Threat Mitigation
Rolletto employs TLS 1.2+ encryption for all login transmissions, ensuring that passwords are encrypted in transit. The stored passwords are hashed using SHA-256 with salt, making database breaches less catastrophic. Two-factor authentication (2FA) is optional but recommended; it adds a time-based one-time password (TOTP) generated via an app like Google Authenticator. The login process thus becomes: 1) Enter email/password, 2) Input 6-digit TOTP, 3) Session granted. Threat mitigation includes monitoring for IP anomalies—if you login from a different country suddenly, Rolletto may require email re-confirmation. This security stack protects the rolletto online ecosystem from common attacks like phishing and credential stuffing.
Troubleshooting Login Issues: Scenarios & Solutions
Common login failures and their technical resolutions:
- „Invalid Password“ Error: Often due to browser caching corrupted passwords. Clear browser cache or try the rolletto app. If persistent, use password reset via email—ensure the reset link is accessed within 10 minutes as it expires.
- Account Locked Message: Usually from exceeding failed attempts. Wait 15 minutes for automatic unlock. If not, contact support with your registered email.
- App Login Crash: On the rolletto app, if login button crashes, check app version (update to latest) or reinstall. This is often a local storage corruption issue.
- Email Verification Not Received: Check email spam folder; if missing, the registration email might be incorrect. Re-register with a correct email.
- Session Expiry During Play: Extend session duration in account settings or enable „persistent login“ in the app, but be aware of security risks.
Advanced scenario: Suppose you login successfully but games don’t load. This may be a session token mismatch between login and game server. Solution: Logout completely, clear cookies, and login again to generate fresh tokens.
Extended FAQ: Rolletto Login Queries
Q1: Can I use the same login for both Rolletto website and app?
Yes, the login credentials are unified. However, simultaneous sessions on both may cause token conflicts; it’s best to use one at a time.
Q2: What happens if I lose my 2FA device?
Contact Rolletto support with your registered email. They will disable 2FA after identity verification, allowing password-only login temporarily.
Q3: Why does Rolletto sometimes ask for my birthday during login?
This is a random security check to prevent automated bots. It verifies account details against stored data.
Q4: Is there a login attempt limit?
Yes, 5 failed attempts within 15 minutes triggers a lockout. This is a security measure against brute-force attacks.
Q5: How do I change my login email?
You cannot change email directly; it’s your primary identifier. You must create a new account with the new email.
Q6: Does the rolletto app store my password locally?
No, the app stores only a session token. The password is never saved on the device; it’s transmitted securely to servers.
Q7: What if I login from a different country?
Rolletto may flag this as suspicious and require email verification. Ensure your email is accessible to bypass this.
Q8: Can I login without an internet connection?
No, both rolletto online and app require active internet for authentication against central servers.
Q9: Are login details encrypted?
Yes, during transmission via TLS. At rest, passwords are hashed with SHA-256.
Q10: How long does a login session last?
Default is 30 minutes, but in the rolletto app, you can extend to 24 hours in settings for convenience.
Mastering the Rolletto login process involves understanding these technical nuances. From registration to daily access, each step is designed for security and user convenience. By following this guide, you can navigate the rolletto online platform with confidence, ensuring that your login remains secure and functional across all devices. Regular updates to passwords and embracing 2FA will further fortify your account against evolving digital threats.

Neueste Kommentare